Manage your Snowplow account using the Credentials API
You can control Snowplow Console (e.g., to automate certain actions) through its API. To use this API, you need to first obtain an API token.
Create an API key
In Console, navigate to Settings > Manage organization > API keys for managing Snowplow. To view this page, you need a View API keys permission.
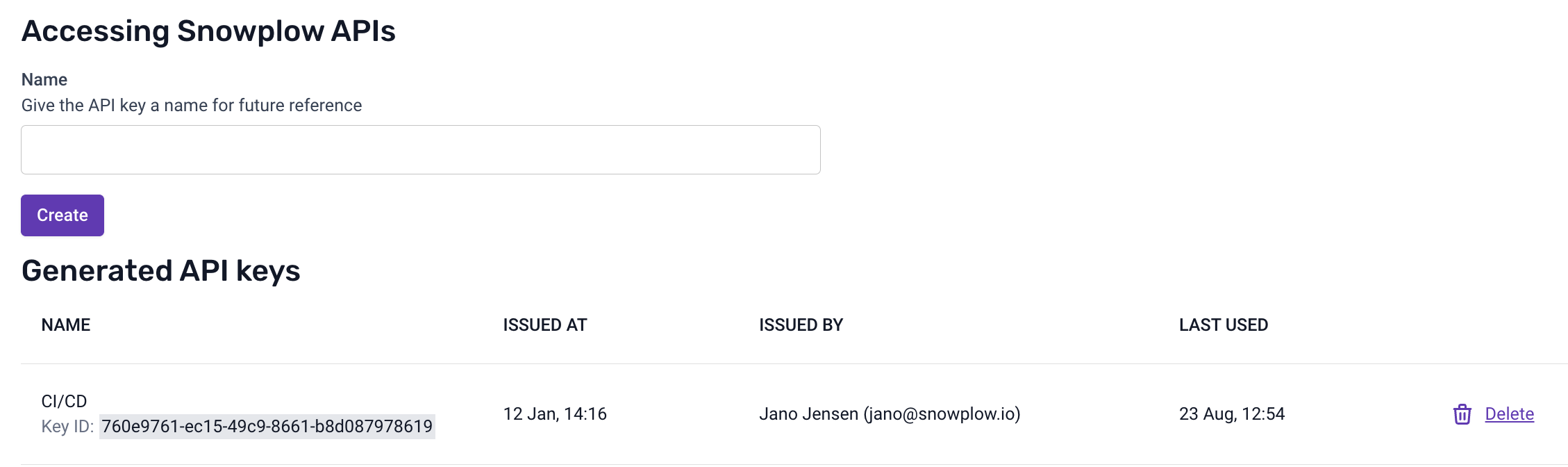
You can create multiple API keys. It's also possible to delete any key.
When you create an API key, store the API key ID and the API key itself in a secure location. This pair works like a combination of a username and password, and you should treat it with the same level of security.
All API keys have admin privileges. Do not share these keys with people or systems you do not trust.
Obtain an access token
Once you have an API key and key ID, you can exchange them for a temporary access token valid for 24 hours.
For example, using curl, the process would look like this:
curl \
--header 'X-API-Key-ID: <API_KEY_ID>' \
--header 'X-API-Key: <API_KEY>' \
https://console.snowplowanalytics.com/api/msc/v1/organizations/<ORGANIZATION_ID>/credentials/v3/token
Previous versions
A previous version of the token exchange endpoint is still available, only requiring the API key:
curl \
--header 'X-API-Key: <API_KEY>' \
https://console.snowplowanalytics.com/api/msc/v1/organizations/<ORGANIZATION_ID>/credentials/v2/token
This endpoint is deprecated and will be removed in the future. Use the v3 endpoint detailed above instead.
You can find your Organization ID on the Manage organization page in Console.
The curl command above will return a JWT as follows:
{ "accessToken": "<JWT>" }
Use the access token with Console API
You can use the access token to supply authorization headers for subsequent API requests:
curl --header 'Authorization: Bearer <JWT>'