Snowplow Inspector
We highly recommend using the Snowplow Inspector Chrome extension for validating your tracking code.
Once you add the extension to Chrome, you can view it by opening Developer Tools (usually Ctrl+Shift+I or on Mac Cmd+Option+I), where it has its own tab named ‘Snowplow’ (look for the tab adjacent to ‘Elements’, ‘Console’, ‘Network’, etc. - it may be necessary to expand the list of tabs using the » button).
The code for the Snowplow Inspector is in GitHub. To install the extension in Firefox, use the .xpi file from the Releases page.
How it works
As a user browses a webpage they can perform different actions that may be tracked as Snowplow events. These events are sent as HTTP requests to the Snowplow collector that the tracker on the webpage is pointed towards. Simply put, what the Snowplow Inspector extension does is parse these HTTP requests into a more easily readable format. This allows anyone with the extension to more easily see what actions on a webpage with Snowplow tracking trigger events to be sent to a Snowplow pipeline.
In the example below two events were fired as HTTP post requests from a test webpage: a page_view event and a (self-describing) link_click event.
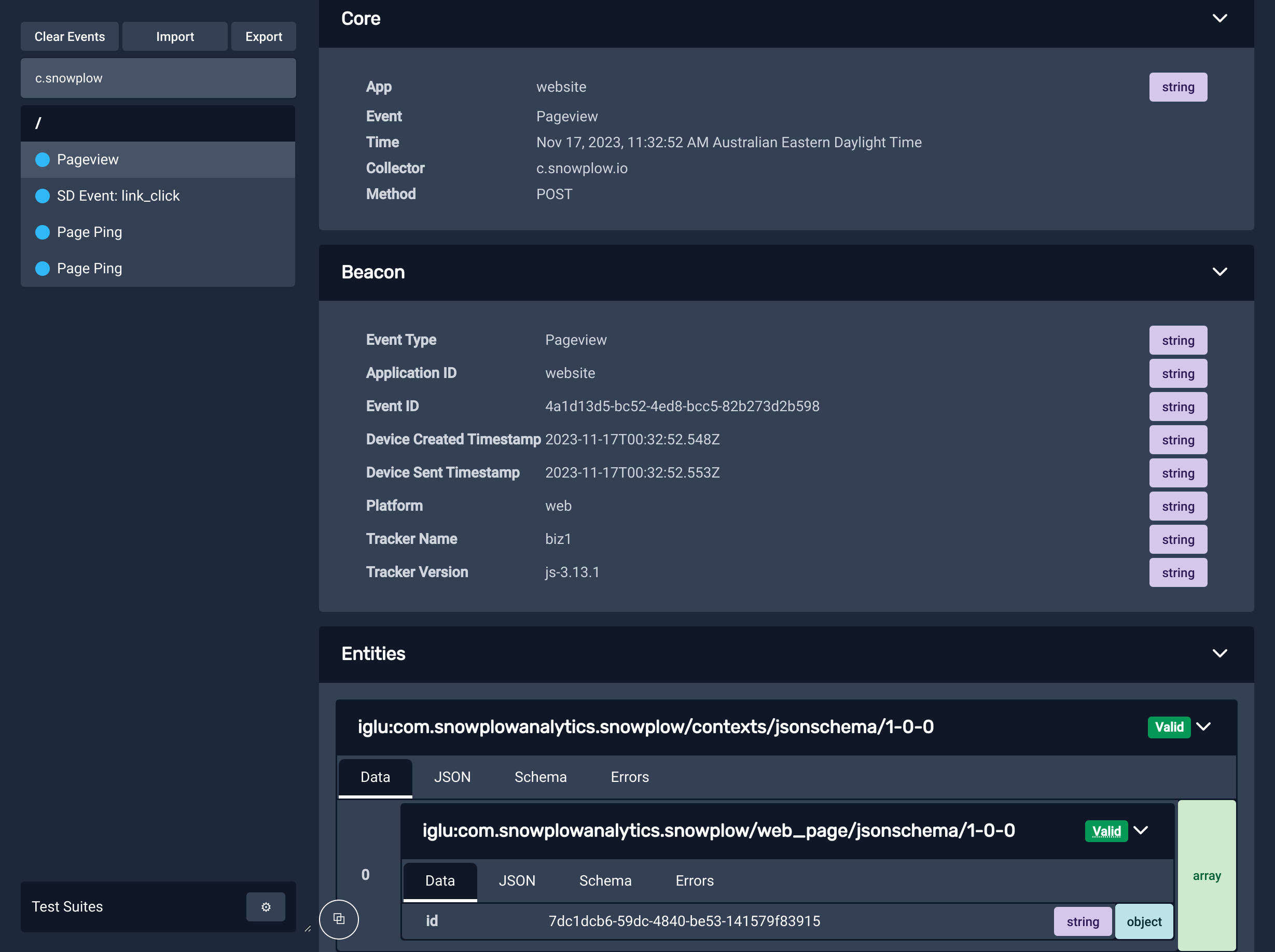
Within the parsed out HTTP requests that comprise the event payload are a variety of Snowplow canonical event fields such as unique event_id, timestamps, and user and session identifiers, as well as any custom Event or Entity fields.
The role of Snowplow Inspector in event QA
The Snowplow Inspector extension is an invaluable tool for anyone who is pushing tracking live as it gives real time - easy to access - information on which events are being emitted and what the contents of these events are. This makes the tool a good first port of call when trying to answer questions such as “why is X event not appearing in my data warehouse” by showing whether or not the event is actually firing on a chosen webpage.
Additionally, you can configure the extension to show whether or not an event has passed validation according to any event validation rules codified in the corresponding schema.
For events that failed validation in production historically that you are unable to replicate in your own browser, see our guides on how to query failed events from their respective destinations. These failed events have a specific format that includes an array of helpful, detailed error messages that explain the exact reasons why the event failed validation. These events can also be imported into the extension to view as if your browser had generated them itself.